Kasada, Shape, and the Next Generation of Anti-Bot: What Scrapers Need to Know


The Scraper
Bypass Methods
Cloudflare and DataDome get all the attention. They're the names you see in scrapers' Discord channels, the ones with active bypass threads and community-maintained workarounds. And they're genuinely hard to beat consistently.
But if you're working in financial services, travel, healthcare, or high-value retail, you're increasingly hitting something different. Something that doesn't announce itself in response headers. Something that lets your request through, and silently logs everything wrong with it.
This is the tier above Cloudflare. It's time to understand it.
Why the Next-Gen Vendors Are Different
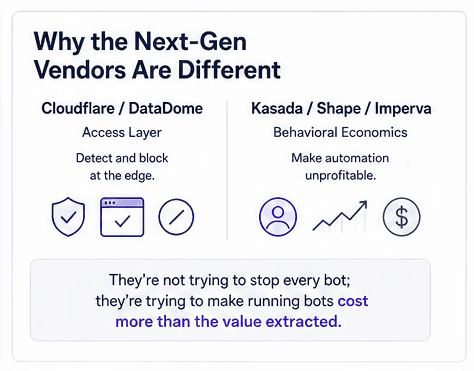
Kasada, Shape Security (now F5 Distributed Cloud Bot Defense), and Imperva Advanced Bot Protection represent a different philosophy from the commodity anti-bot market.
Cloudflare and DataDome focus primarily on the access layer: TLS fingerprinting, IP reputation, browser challenge pages, CAPTCHA gates. Their model is defensive perimeter, detect and block at the edge.
The next-generation vendors focus primarily on behavioral economics: making automation unprofitable rather than technically impossible. They're not trying to stop every bot; they're trying to make running bots against their clients' properties cost more than the value extracted.
The implications for scrapers are significant. These systems are designed to let you think you're succeeding while collecting evidence.
Kasada: The Proof-of-Work Philosophy
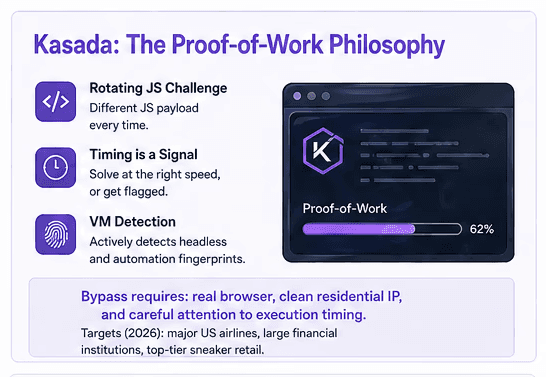
Kasada's core mechanism is a client-side proof-of-work challenge embedded in a JavaScript payload. When your browser (or headless browser) loads a Kasada-protected page, it downloads an obfuscated JS bundle that:
Performs cryptographic work: hashing operations that take measurable CPU time to complete
Collects environmental signals: browser API availability, timing patterns, canvas fingerprint
Constructs a signed token submitted with the actual request
The key properties that make Kasada hard to bypass:
The JS payload rotates. Kasada doesn't serve the same challenge code twice. The JS bundle changes with each deployment cycle. Reverse-engineering the current challenge logic and hardcoding the solution is a treadmill, not a one-time fix.
Timing is a signal. The proof-of-work is calibrated to human browser execution timing. Complete it too fast (as a native solver would) and the token is flagged. The challenge isn't just "solve this", it's "solve this at the right speed."
VM detection. The JS bundle actively probes for headless browser indicators: missing APIs, inconsistent timing, canvas/WebGL rendering anomalies. Node.js environments and default Chromium headless configurations have well-known fingerprint profiles that Kasada's detection has mapped.
The bypass approach that works requires: a full-browser execution environment (real Chromium or a purpose-built anti-detect browser), a residential IP with a clean reputation, and careful attention to execution timing. Even then, Kasada-protected targets should be treated as high-cost targets that require maximum investment in IP quality and browser authenticity.
Targets using Kasada as of 2026: major US airlines, several large financial institutions, top-tier sneaker retail.
Shape Security / F5: The Behavioral Graph
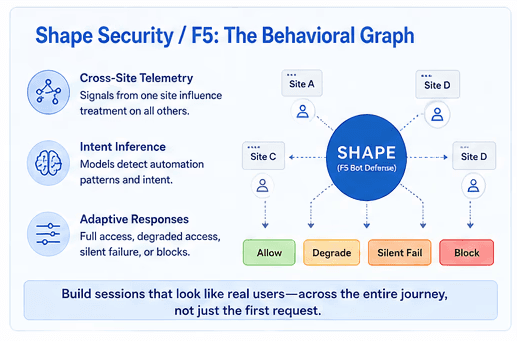
Shape (now operating as F5 Distributed Cloud Bot Defense post-acquisition) takes a different approach. Rather than a client-side challenge, Shape builds a behavioral graph across sessions, users, and organizations.
Shape doesn't just analyze your request in isolation. It analyzes your request in the context of every other request it has ever seen from your IP range, your AS number, your browser fingerprint cluster, and patterns that correlate with known automation infrastructure.
Key capabilities:
Cross-site telemetry. Shape's client network means that if your automation has been flagged on one F5 customer's property, that signal may influence your treatment on every other F5 customer's property. You don't start fresh with each target.
Intent inference. Shape's models are trained on both automation patterns and legitimate user patterns. High add-to-cart rates with no browsing behavior, velocity patterns inconsistent with human navigation, session sequences that match known bot playbooks, all of these feed a risk score that shapes the response.
Adaptive responses. Shape doesn't just block. Depending on risk score, a session might receive full access, degraded access (slower responses, stale data, reduced search results), silent failure (requests succeed but nothing is stored), or hard blocks. The operator can tune the response per risk tier.
The implication: Shape-protected targets are most effectively approached by building sessions that are behaviorally indistinguishable from genuine users over time. Not just the first request, the full session arc from entry to exit. This requires browser automation that models human reading patterns, scroll behavior, dwell time variance, and navigation logic.
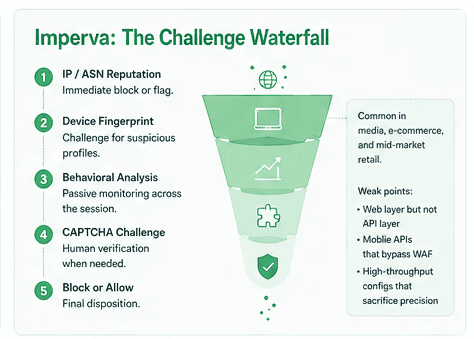
Imperva: The Challenge Waterfall
Imperva Advanced Bot Protection combines IP reputation, device fingerprinting, behavioral analysis, and CAPTCHA challenge in a layered system, what their documentation calls a "challenge waterfall."
The waterfall works in tiers:
IP/ASN reputation: immediate block or flag for known datacenter ranges, Tor exit nodes, and flagged residential ranges
Device fingerprint: challenge issuance for suspicious browser profiles
Behavioral analysis: passive monitoring for automation signals across the session
CAPTCHA challenge: human verification for sessions that pass device checks but fail behavioral thresholds
Block or allow: final disposition
Imperva is more common in media, e-commerce, and mid-market retail than in the top-tier financial/travel segment. It's harder to bypass than Cloudflare but generally more consistent, the detection logic changes more slowly than Kasada's rotating challenges, which means community knowledge about bypass approaches stays valid longer.
The known weak points in Imperva configurations: sites that implement Imperva on the web layer but not the API layer, mobile API endpoints that bypass the WAF, and Imperva configurations tuned for high throughput that sacrifice precision for performance.
What All Three Have in Common
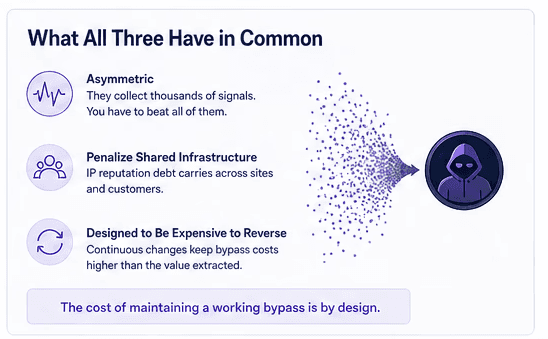
The next-gen vendors share a few structural properties that define the bypass challenge:
They're asymmetric. These systems collect thousands of signals per request. Beating a single signal doesn't help, you need to beat the aggregate. The detection model sees the whole picture; your bypass needs to address all of it simultaneously.
They penalize shared infrastructure. Proxies used heavily by other bot operators accumulate reputation debt on these systems' cross-site telemetry. An IP that's clean on Cloudflare's IP reputation list may already be flagged in Shape's behavioral graph. Pool hygiene matters more against these vendors than against commodity anti-bot.
They're designed to be expensive to reverse. Kasada rotates its code. Shape evolves its behavioral models continuously. Imperva's challenge waterfall adapts based on observed attack patterns. The cost of maintaining a working bypass is designed to exceed the value extracted from most scraping use cases.
The Proxy Strategy for High-Stakes Targets
Against Kasada and Shape in particular, IP quality isn't optional, it's the primary lever. These systems treat IP reputation as a strong prior. A clean residential IP from a legitimate ISP, with no cross-site automation history, arrives with low risk scores. A residential IP that's been used heavily against other protected targets, or that sits in an ASN range associated with proxy services, arrives flagged.
This is the core argument for ethical, consent-based residential pools with genuine network diversity. Evomi's premium residential proxies provide a higher-quality IP subset specifically suited to high-trust targets, IPs with clean reputation profiles across the major bot-detection networks, sourced through legitimate opt-in programs. For Kasada or Shape-protected targets, this is the tier to use, not the entry-level residential pool.
The free trial lets you benchmark performance on your specific target before committing.
The Honest Assessment
Against Kasada in particular: there is no consistently reliable automated bypass that doesn't require significant investment in browser authenticity and IP quality. Anyone selling a "Kasada bypass tool" that works at scale is either operating on a short timeline before the detection adapts, or hasn't tested it on well-configured implementations.
Shape is somewhat more addressable with careful behavioral modeling, but the cross-site telemetry means IP reputation is load-bearing in a way it isn't for simpler systems.
These targets exist on a spectrum from "worth the engineering investment" to "not economically viable to scrape." Most financial and airline data is in the former category, the value is high enough that the bypass investment pencils out. Most mid-tier retail is in the middle, it's possible but expensive, and API access or licensed data may be more practical.
The important thing is entering these engagements with an accurate picture of what you're facing. Treating a Kasada-protected target like a Cloudflare Free tier target will burn proxies, waste compute, and produce nothing useful. Know your opponent.

Author
The Scraper
Engineer and Webscraping Specialist
About Author
The Scraper is a software engineer and web scraping specialist, focused on building production-grade data extraction systems. His work centers on large-scale crawling, anti-bot evasion, proxy infrastructure, and browser automation. He writes about real-world scraping failures, silent data corruption, and systems that operate at scale.