Mobile Is the Last Undefended Frontier (And It Won't Last)


The Scraper
Bypass Methods
While the scraping industry spent the last three years obsessing over Cloudflare bypasses and TLS fingerprint evasion, a quieter opportunity has been hiding in plain sight: mobile apps.
The same companies that serve hardened, bot-resistant web interfaces are running mobile backends that, in many cases, haven't been touched since 2019. No behavioral analysis. No browser fingerprinting. Sometimes no rate limiting worth the name.
This window is closing. Understanding it before it does is the entire point of this post.
Why Mobile APIs Are Different
The core insight: mobile apps talk to APIs, not web pages. When your iPhone opens a travel app and searches for flights, it's hitting a JSON endpoint directly, no JavaScript rendering, no DOM manipulation, no browser fingerprint to check. The anti-bot stack that guards the web frontend often simply doesn't exist on the mobile backend.
This happens for a few structural reasons:
The web and mobile teams at most companies are separate. The web team adopted Cloudflare or DataDome after getting hammered by scrapers. The mobile team's API is behind an API gateway, authenticated with a token, and the assumption, often unstated, is that only the official app talks to it.
That assumption is wrong, and it's been wrong for years. The official app is just a client. Anyone who can reverse engineer its communication protocol can be that client.
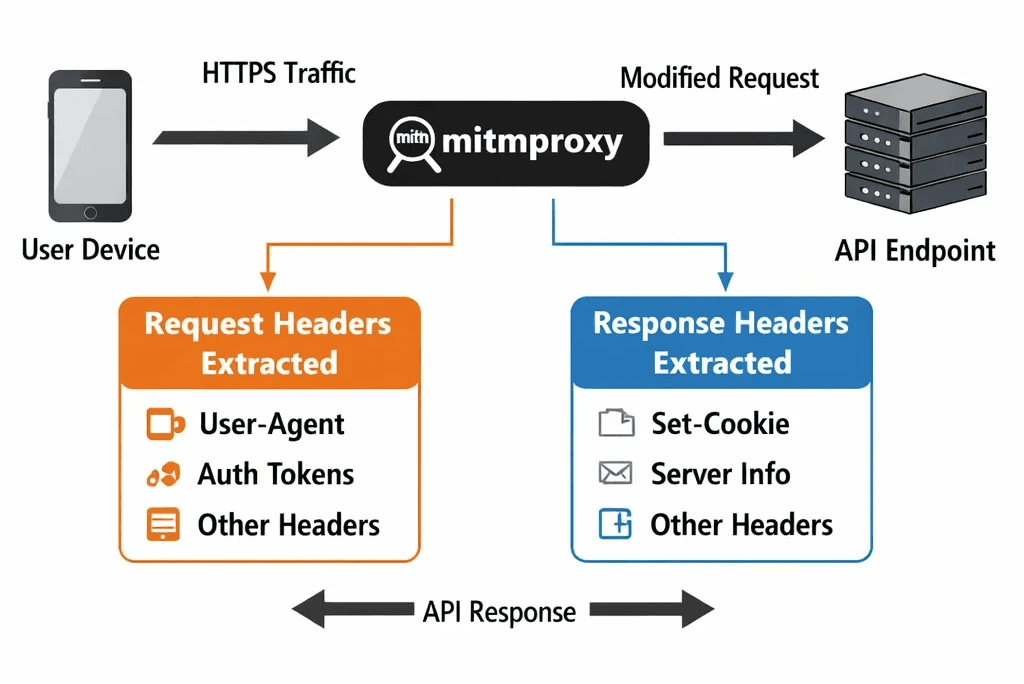
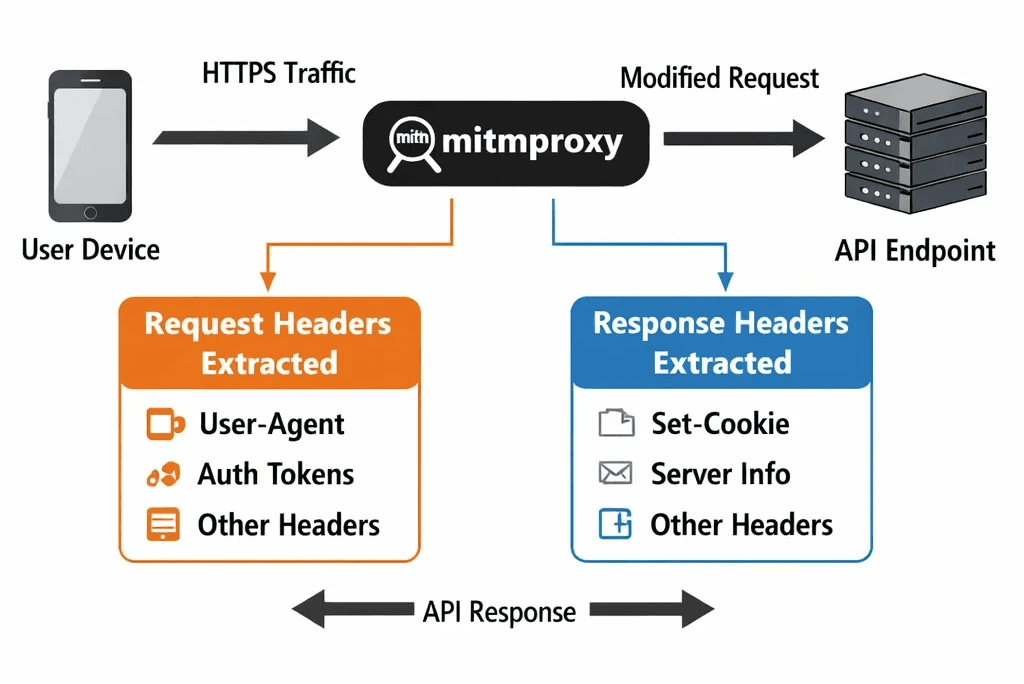
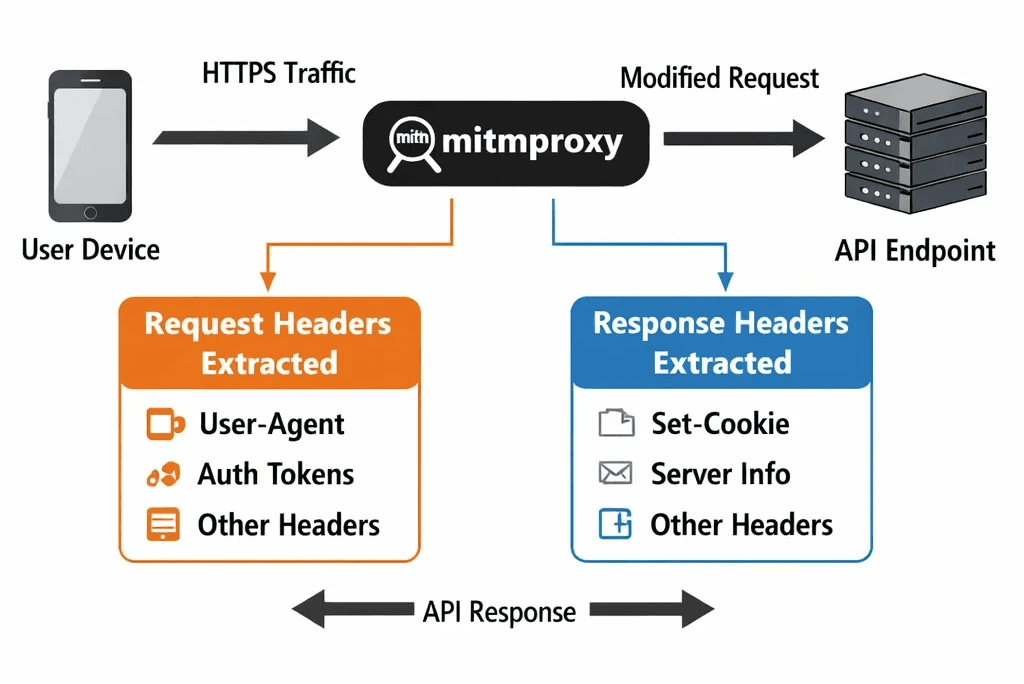
The second factor is certificate pinning, or more accurately, the lack of it. Many mobile apps skip SSL pinning to reduce complexity and support third-party SDKs that need network access. Without pinning, a proxy positioned as a machine-in-the-middle can see all traffic in plaintext. Including the API endpoints, the authentication tokens, and the full request/response structure.
The Toolkit
mitmproxy
mitmproxy is your starting point. It's an open-source HTTPS proxy that lets you intercept, inspect, and modify traffic in real time. With a rooted Android device or an emulator, you install the mitmproxy certificate as a trusted CA, route traffic through it, and watch the app's API calls in the console.
# Start mitmproxy with web UI mitmproxy --web-port 8081 # Or headless for scripting mitmdump -s intercept_script.py
For an Android emulator:
# Route emulator traffic through mitmproxy emulator -avd Pixel_6_API_33 -http-proxy 127.0.0.1:8080
You'll see every API call the app makes. Endpoints, headers, authentication tokens, query parameters, everything. For apps without SSL pinning, this alone is often sufficient to map out the full API surface.
Frida
When SSL pinning is in play, Frida is the tool. Frida is a dynamic instrumentation toolkit that lets you inject JavaScript into a running app process and hook into native functions at runtime. The standard use case for scrapers: intercept the SSL pinning check functions and return success regardless of the certificate.
# Install frida-tools pip install frida-tools # List running processes on connected device frida-ps -U # Run a script against the target app frida -U -l ssl_unpinning.js -f com.target.app
The ssl_unpinning.js scripts that work against most apps are maintained in public repos, the Frida CodeShare repository has community-maintained hooks for OkHttp, TrustKit, Conscrypt, and a dozen other common pinning implementations. For custom implementations, you're hooking javax.net.ssl.X509TrustManager directly.
After unpinning, route the device through mitmproxy. You now see everything.
Reading the API
Once you have full visibility into the API traffic, the next step is pattern extraction:
What are the base endpoints?
What authentication scheme is in use? (Bearer token? API key in header? HMAC-signed requests?)
How are tokens obtained and refreshed?
What rate limiting is visible from response headers?
Are there device attestation headers? (
X-Device-ID,X-App-Version,X-Integrity-Token)
Map this manually for the first session, then build your scraper to replicate the request profile. You're not scraping HTML, you're calling a JSON API with the right headers. It's often faster and more stable than any browser-based approach.
The Coming Wall
This window won't stay open. The mobile security industry is catching up, driven by two converging pressures:
Google Play Integrity API (formerly SafetyNet) provides a hardware-backed attestation signal that tells backend servers whether the request is coming from an unmodified, certified Android device. Apps that implement Play Integrity checks can detect rooted devices, emulators, and sideloaded APKs and refuse to issue tokens to them. As of 2026, adoption is accelerating among travel, finance, and social media apps.
iOS DeviceCheck and App Attest provide the equivalent on Apple's side. App Attest in particular generates a cryptographically signed assertion that the app is a genuine, unmodified Apple build running on real hardware. It's nearly impossible to spoof without a jailbroken device running on a genuinely enrolled Apple ID, a narrowing attack surface.
Obfuscation layers are also increasing. Tools like DexGuard and R8 with aggressive mode make static analysis harder. Runtime obfuscation of API keys and tokens is becoming standard. Some apps implement custom HMAC request signing that requires either extracting the signing key from the binary or running the actual app code to generate valid signatures.
The mobile frontier isn't going away, it's getting hardened. The engineers who mapped it in 2024-2026 will have a structural advantage over those who try to enter in 2028.
The Infrastructure Layer
Mobile scraping introduces a distinct infrastructure requirement: traffic should look like mobile traffic. Sending API requests from a datacenter IP to a mobile-only endpoint is a trivial detection signal. The source IP should match the expected network profile for a real user of the app.
This is where Evomi's mobile proxies are purpose-built for this use case, real 4G/5G device IPs from genuine mobile carriers, with the ASN profile, geolocation, and network characteristics that mobile API backends expect. When you're replicating a mobile client, the proxy layer needs to match. A residential IP from a fiber ISP is better than a datacenter IP, but a genuine mobile IP is better still.
You can test Evomi's mobile proxies with a free trial before committing to volume.
What the Stack Looks Like
A production mobile scraping setup in 2026:
Android emulator (or rooted physical device) as the traffic origin
Frida for runtime SSL unpinning on pinned apps
mitmproxy for traffic interception and request mapping
Python +
httpxorrequeststo replicate API calls with extracted headersMobile proxy rotation (Evomi mobile) to match source IP to expected network profile
Token refresh logic to handle authentication expiry
Rate limiting aligned to app behavior, don't hammer an endpoint the app hits once per session
The extraction layer in mobile scraping is often simpler than web, clean JSON responses, predictable schemas, no DOM parsing required. The complexity is in the access layer: replicating a legitimate mobile client convincingly enough that the backend sees what it expects.
The Honest Assessment
Mobile scraping is higher-friction to set up than web scraping. Device management, APK analysis, Frida scripting, these are non-trivial. But once the API surface is mapped and the request replication is working, the data pipeline is often more reliable than browser-based web scraping. No rendering, no JavaScript execution, no DOM changes to chase.
The window is open. It's narrowing. The teams that understand mobile API extraction now will have capabilities that aren't accessible to teams who wait until the attestation walls are fully built.
The clock is running.
While the scraping industry spent the last three years obsessing over Cloudflare bypasses and TLS fingerprint evasion, a quieter opportunity has been hiding in plain sight: mobile apps.
The same companies that serve hardened, bot-resistant web interfaces are running mobile backends that, in many cases, haven't been touched since 2019. No behavioral analysis. No browser fingerprinting. Sometimes no rate limiting worth the name.
This window is closing. Understanding it before it does is the entire point of this post.
Why Mobile APIs Are Different
The core insight: mobile apps talk to APIs, not web pages. When your iPhone opens a travel app and searches for flights, it's hitting a JSON endpoint directly, no JavaScript rendering, no DOM manipulation, no browser fingerprint to check. The anti-bot stack that guards the web frontend often simply doesn't exist on the mobile backend.
This happens for a few structural reasons:
The web and mobile teams at most companies are separate. The web team adopted Cloudflare or DataDome after getting hammered by scrapers. The mobile team's API is behind an API gateway, authenticated with a token, and the assumption, often unstated, is that only the official app talks to it.
That assumption is wrong, and it's been wrong for years. The official app is just a client. Anyone who can reverse engineer its communication protocol can be that client.
The second factor is certificate pinning, or more accurately, the lack of it. Many mobile apps skip SSL pinning to reduce complexity and support third-party SDKs that need network access. Without pinning, a proxy positioned as a machine-in-the-middle can see all traffic in plaintext. Including the API endpoints, the authentication tokens, and the full request/response structure.
The Toolkit
mitmproxy
mitmproxy is your starting point. It's an open-source HTTPS proxy that lets you intercept, inspect, and modify traffic in real time. With a rooted Android device or an emulator, you install the mitmproxy certificate as a trusted CA, route traffic through it, and watch the app's API calls in the console.
# Start mitmproxy with web UI mitmproxy --web-port 8081 # Or headless for scripting mitmdump -s intercept_script.py
For an Android emulator:
# Route emulator traffic through mitmproxy emulator -avd Pixel_6_API_33 -http-proxy 127.0.0.1:8080
You'll see every API call the app makes. Endpoints, headers, authentication tokens, query parameters, everything. For apps without SSL pinning, this alone is often sufficient to map out the full API surface.
Frida
When SSL pinning is in play, Frida is the tool. Frida is a dynamic instrumentation toolkit that lets you inject JavaScript into a running app process and hook into native functions at runtime. The standard use case for scrapers: intercept the SSL pinning check functions and return success regardless of the certificate.
# Install frida-tools pip install frida-tools # List running processes on connected device frida-ps -U # Run a script against the target app frida -U -l ssl_unpinning.js -f com.target.app
The ssl_unpinning.js scripts that work against most apps are maintained in public repos, the Frida CodeShare repository has community-maintained hooks for OkHttp, TrustKit, Conscrypt, and a dozen other common pinning implementations. For custom implementations, you're hooking javax.net.ssl.X509TrustManager directly.
After unpinning, route the device through mitmproxy. You now see everything.
Reading the API
Once you have full visibility into the API traffic, the next step is pattern extraction:
What are the base endpoints?
What authentication scheme is in use? (Bearer token? API key in header? HMAC-signed requests?)
How are tokens obtained and refreshed?
What rate limiting is visible from response headers?
Are there device attestation headers? (
X-Device-ID,X-App-Version,X-Integrity-Token)
Map this manually for the first session, then build your scraper to replicate the request profile. You're not scraping HTML, you're calling a JSON API with the right headers. It's often faster and more stable than any browser-based approach.
The Coming Wall
This window won't stay open. The mobile security industry is catching up, driven by two converging pressures:
Google Play Integrity API (formerly SafetyNet) provides a hardware-backed attestation signal that tells backend servers whether the request is coming from an unmodified, certified Android device. Apps that implement Play Integrity checks can detect rooted devices, emulators, and sideloaded APKs and refuse to issue tokens to them. As of 2026, adoption is accelerating among travel, finance, and social media apps.
iOS DeviceCheck and App Attest provide the equivalent on Apple's side. App Attest in particular generates a cryptographically signed assertion that the app is a genuine, unmodified Apple build running on real hardware. It's nearly impossible to spoof without a jailbroken device running on a genuinely enrolled Apple ID, a narrowing attack surface.
Obfuscation layers are also increasing. Tools like DexGuard and R8 with aggressive mode make static analysis harder. Runtime obfuscation of API keys and tokens is becoming standard. Some apps implement custom HMAC request signing that requires either extracting the signing key from the binary or running the actual app code to generate valid signatures.
The mobile frontier isn't going away, it's getting hardened. The engineers who mapped it in 2024-2026 will have a structural advantage over those who try to enter in 2028.
The Infrastructure Layer
Mobile scraping introduces a distinct infrastructure requirement: traffic should look like mobile traffic. Sending API requests from a datacenter IP to a mobile-only endpoint is a trivial detection signal. The source IP should match the expected network profile for a real user of the app.
This is where Evomi's mobile proxies are purpose-built for this use case, real 4G/5G device IPs from genuine mobile carriers, with the ASN profile, geolocation, and network characteristics that mobile API backends expect. When you're replicating a mobile client, the proxy layer needs to match. A residential IP from a fiber ISP is better than a datacenter IP, but a genuine mobile IP is better still.
You can test Evomi's mobile proxies with a free trial before committing to volume.
What the Stack Looks Like
A production mobile scraping setup in 2026:
Android emulator (or rooted physical device) as the traffic origin
Frida for runtime SSL unpinning on pinned apps
mitmproxy for traffic interception and request mapping
Python +
httpxorrequeststo replicate API calls with extracted headersMobile proxy rotation (Evomi mobile) to match source IP to expected network profile
Token refresh logic to handle authentication expiry
Rate limiting aligned to app behavior, don't hammer an endpoint the app hits once per session
The extraction layer in mobile scraping is often simpler than web, clean JSON responses, predictable schemas, no DOM parsing required. The complexity is in the access layer: replicating a legitimate mobile client convincingly enough that the backend sees what it expects.
The Honest Assessment
Mobile scraping is higher-friction to set up than web scraping. Device management, APK analysis, Frida scripting, these are non-trivial. But once the API surface is mapped and the request replication is working, the data pipeline is often more reliable than browser-based web scraping. No rendering, no JavaScript execution, no DOM changes to chase.
The window is open. It's narrowing. The teams that understand mobile API extraction now will have capabilities that aren't accessible to teams who wait until the attestation walls are fully built.
The clock is running.
While the scraping industry spent the last three years obsessing over Cloudflare bypasses and TLS fingerprint evasion, a quieter opportunity has been hiding in plain sight: mobile apps.
The same companies that serve hardened, bot-resistant web interfaces are running mobile backends that, in many cases, haven't been touched since 2019. No behavioral analysis. No browser fingerprinting. Sometimes no rate limiting worth the name.
This window is closing. Understanding it before it does is the entire point of this post.
Why Mobile APIs Are Different
The core insight: mobile apps talk to APIs, not web pages. When your iPhone opens a travel app and searches for flights, it's hitting a JSON endpoint directly, no JavaScript rendering, no DOM manipulation, no browser fingerprint to check. The anti-bot stack that guards the web frontend often simply doesn't exist on the mobile backend.
This happens for a few structural reasons:
The web and mobile teams at most companies are separate. The web team adopted Cloudflare or DataDome after getting hammered by scrapers. The mobile team's API is behind an API gateway, authenticated with a token, and the assumption, often unstated, is that only the official app talks to it.
That assumption is wrong, and it's been wrong for years. The official app is just a client. Anyone who can reverse engineer its communication protocol can be that client.
The second factor is certificate pinning, or more accurately, the lack of it. Many mobile apps skip SSL pinning to reduce complexity and support third-party SDKs that need network access. Without pinning, a proxy positioned as a machine-in-the-middle can see all traffic in plaintext. Including the API endpoints, the authentication tokens, and the full request/response structure.
The Toolkit
mitmproxy
mitmproxy is your starting point. It's an open-source HTTPS proxy that lets you intercept, inspect, and modify traffic in real time. With a rooted Android device or an emulator, you install the mitmproxy certificate as a trusted CA, route traffic through it, and watch the app's API calls in the console.
# Start mitmproxy with web UI mitmproxy --web-port 8081 # Or headless for scripting mitmdump -s intercept_script.py
For an Android emulator:
# Route emulator traffic through mitmproxy emulator -avd Pixel_6_API_33 -http-proxy 127.0.0.1:8080
You'll see every API call the app makes. Endpoints, headers, authentication tokens, query parameters, everything. For apps without SSL pinning, this alone is often sufficient to map out the full API surface.
Frida
When SSL pinning is in play, Frida is the tool. Frida is a dynamic instrumentation toolkit that lets you inject JavaScript into a running app process and hook into native functions at runtime. The standard use case for scrapers: intercept the SSL pinning check functions and return success regardless of the certificate.
# Install frida-tools pip install frida-tools # List running processes on connected device frida-ps -U # Run a script against the target app frida -U -l ssl_unpinning.js -f com.target.app
The ssl_unpinning.js scripts that work against most apps are maintained in public repos, the Frida CodeShare repository has community-maintained hooks for OkHttp, TrustKit, Conscrypt, and a dozen other common pinning implementations. For custom implementations, you're hooking javax.net.ssl.X509TrustManager directly.
After unpinning, route the device through mitmproxy. You now see everything.
Reading the API
Once you have full visibility into the API traffic, the next step is pattern extraction:
What are the base endpoints?
What authentication scheme is in use? (Bearer token? API key in header? HMAC-signed requests?)
How are tokens obtained and refreshed?
What rate limiting is visible from response headers?
Are there device attestation headers? (
X-Device-ID,X-App-Version,X-Integrity-Token)
Map this manually for the first session, then build your scraper to replicate the request profile. You're not scraping HTML, you're calling a JSON API with the right headers. It's often faster and more stable than any browser-based approach.
The Coming Wall
This window won't stay open. The mobile security industry is catching up, driven by two converging pressures:
Google Play Integrity API (formerly SafetyNet) provides a hardware-backed attestation signal that tells backend servers whether the request is coming from an unmodified, certified Android device. Apps that implement Play Integrity checks can detect rooted devices, emulators, and sideloaded APKs and refuse to issue tokens to them. As of 2026, adoption is accelerating among travel, finance, and social media apps.
iOS DeviceCheck and App Attest provide the equivalent on Apple's side. App Attest in particular generates a cryptographically signed assertion that the app is a genuine, unmodified Apple build running on real hardware. It's nearly impossible to spoof without a jailbroken device running on a genuinely enrolled Apple ID, a narrowing attack surface.
Obfuscation layers are also increasing. Tools like DexGuard and R8 with aggressive mode make static analysis harder. Runtime obfuscation of API keys and tokens is becoming standard. Some apps implement custom HMAC request signing that requires either extracting the signing key from the binary or running the actual app code to generate valid signatures.
The mobile frontier isn't going away, it's getting hardened. The engineers who mapped it in 2024-2026 will have a structural advantage over those who try to enter in 2028.
The Infrastructure Layer
Mobile scraping introduces a distinct infrastructure requirement: traffic should look like mobile traffic. Sending API requests from a datacenter IP to a mobile-only endpoint is a trivial detection signal. The source IP should match the expected network profile for a real user of the app.
This is where Evomi's mobile proxies are purpose-built for this use case, real 4G/5G device IPs from genuine mobile carriers, with the ASN profile, geolocation, and network characteristics that mobile API backends expect. When you're replicating a mobile client, the proxy layer needs to match. A residential IP from a fiber ISP is better than a datacenter IP, but a genuine mobile IP is better still.
You can test Evomi's mobile proxies with a free trial before committing to volume.
What the Stack Looks Like
A production mobile scraping setup in 2026:
Android emulator (or rooted physical device) as the traffic origin
Frida for runtime SSL unpinning on pinned apps
mitmproxy for traffic interception and request mapping
Python +
httpxorrequeststo replicate API calls with extracted headersMobile proxy rotation (Evomi mobile) to match source IP to expected network profile
Token refresh logic to handle authentication expiry
Rate limiting aligned to app behavior, don't hammer an endpoint the app hits once per session
The extraction layer in mobile scraping is often simpler than web, clean JSON responses, predictable schemas, no DOM parsing required. The complexity is in the access layer: replicating a legitimate mobile client convincingly enough that the backend sees what it expects.
The Honest Assessment
Mobile scraping is higher-friction to set up than web scraping. Device management, APK analysis, Frida scripting, these are non-trivial. But once the API surface is mapped and the request replication is working, the data pipeline is often more reliable than browser-based web scraping. No rendering, no JavaScript execution, no DOM changes to chase.
The window is open. It's narrowing. The teams that understand mobile API extraction now will have capabilities that aren't accessible to teams who wait until the attestation walls are fully built.
The clock is running.

Author
The Scraper
Engineer and Webscraping Specialist
About Author
The Scraper is a software engineer and web scraping specialist, focused on building production-grade data extraction systems. His work centers on large-scale crawling, anti-bot evasion, proxy infrastructure, and browser automation. He writes about real-world scraping failures, silent data corruption, and systems that operate at scale.



